TECH BRIEF

Whether its a phishing scam or an in-cloud attack, enterprises must be ready to protect their IoT systems from malware of all types.
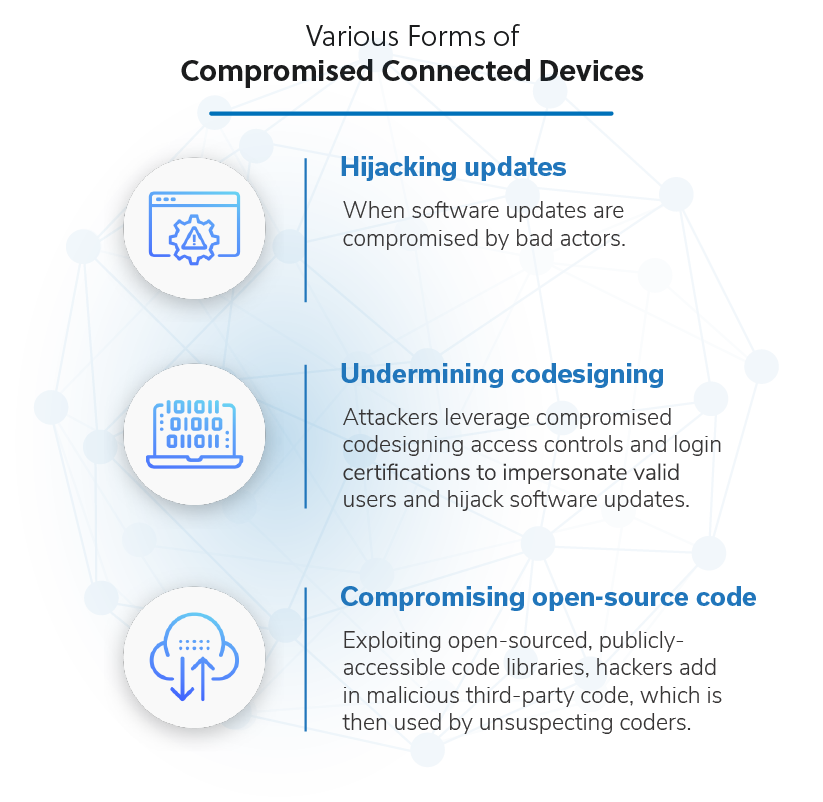
Examine the main ways threat actors try to infect IoT devices and systems with malware.
IoT isn't easy. To build a digital enterprise, you need an Intelligent IoT Network.
